Apple verteilt finale Version von macOS Mojave 10.14.4
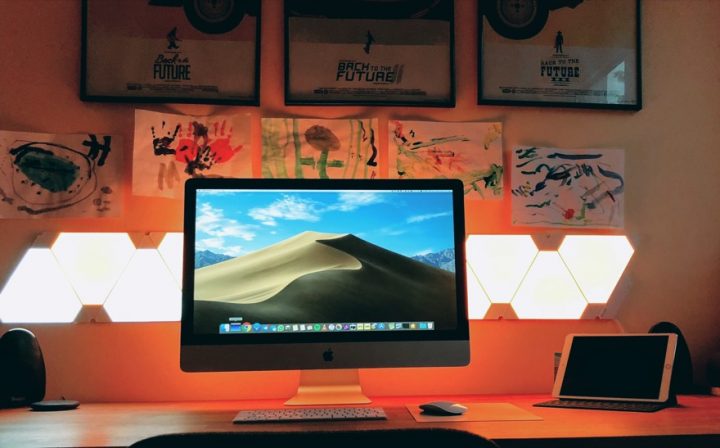
Apple hat gestern nicht nur eine Menge Neuerungen vorgestellt, sondern auch finale Versionen seiner Betriebssysteme verteilt. iOS 12.2 und tvOS 12.2 sind auf dem Weg zum Anwender und auch macOS 10.14.4 steht nun als fertiges Release zum Download bereit.
Apple führt mit dem Update unter anderem den automatischen dunklen Modus und vereinfachte Anmeldungen für Webseiten in Safari ein. Bei Apple Music wurde genau wie unter iOS auch der Entdecken-Tab überarbeitet und ist nun übersichtlicher. Besitzer der neuen AirPods können diese nun auch mit macOS nutzen und vieles mehr. Was aber viel wichtiger ist, dass sind die Fehlerbehebungen und Verbesserungen im Bereich Performance und vor allem Security. Ich habe euch die Changelogs mit in den Artikel getan und die Liste der Security Bugfixes ist wirklich lang.
Wartet also nicht zu lang mit dem Update eurer Macs oder MacBooks.
Release Notes:
Das macOS Mojave 10.14.4-Update enthält Fehlerbehebungen und Verbesserungen, u. a. an der Stabilität und der Zuverlässigkeit deines Mac.
Safari
– Unterstützung für den Modus „Dunkel“ bei Websites, die eigene Farbschemen unterstützen
– Vereinfachte Anmeldung auf Websites, wenn für die Zugangsdaten „Passwort automatisch ausfüllen“ verwendet wird
– Aufforderungen zu Push-Benachrichtigungen erst nach Interaktion mit einer Website zulassen
– Warnhinweis, wenn eine unsichere Website geladen wird
– Entfernung der Unterstützung für den nicht mehr gültigen „Do Not Track“-Standard, um potentiellen Missbrauch als Erkennungsvariable (Fingerprinting) zu verhindern; Intelligent Tracking Prevention verhindert nun standardmäßig websiteübergreifendes Tracking
iTunes
– Anzeige von mehr redaktionellen Highlights auf einer einzelnen Seite im Tab „Entdecken“, um in Apple Music noch einfacher neue Musik, Playlists und mehr entdecken zu können.
AirPods
– Unterstützung für AirPods (2. Generation)
Mehr
– Unterstützung für „Luftqualitätsindex“ in der Karten-App in den USA, Großbritannien und Indien
– Bessere Qualität von Audioaufnahmen in „Nachrichten“
– Verbesserte Unterstützung für externe GPUs in der Aktivitätsanzeige
– Behebung eines App Store-Problems, aufgrund dessen die neuesten Versionen von Pages, Keynote, Numbers, iMovie und GarageBand nicht übernommen werden konnten
– Verbesserte Zuverlässigkeit von USB-Audiogeräten bei Verwendung mit den 2018 eingeführten MacBook Air-, MacBook Pro- und Mac mini-Modellen
– Korrektur der Bildschirmstandardhelligkeit des MacBook Air (Herbst 2018)
– Behebung eines Grafikproblems, das bei manchen an den Mac mini (2018) angeschlossenen externen Displays zu Inkompatibilitäten führen konnte
– Behebung von WLAN-Verbindungsproblemen, die nach dem Upgrade auf macOS Mojave auftreten konnten
– Behebung eines Problems, bei dem erneut hinzugefügte Exchange-Accounts nicht mehr im Bereich „Internetaccounts“ angezeigt wurden
– Behebung eines Problems, bei dem in Mail AOL-Benutzerpasswörter häufig angefordert werden konnten
Security Fixes:
macOS Mojave 10.14.4, Security Update 2019-002 High Sierra, Security Update 2019-002 Sierra
Released March 25, 2019AppleGraphicsControl
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to execute arbitrary code with kernel privileges
Description: A buffer overflow was addressed with improved size validation.
CVE-2019-8555: Zhiyi Zhang of 360 ESG Codesafe Team, Zhuo Liang and shrek_wzw of Qihoo 360 Nirvan Team
Bom
Available for: macOS Mojave 10.14.3
Impact: A malicious application may bypass Gatekeeper checks
Description: This issue was addressed with improved handling of file metadata.
CVE-2019-6239: Ian Moorhouse and Michael Trimm
CFString
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted string may lead to a denial of service
Description: A validation issue was addressed with improved logic.
CVE-2019-8516: SWIPS Team of Frifee Inc.
configd
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8552: Mohamed Ghannam (@_simo36)
Contacts
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2019-8511: an anonymous researcher
CoreCrypto
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2019-8542: an anonymous researcher
DiskArbitration
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: An encrypted volume may be unmounted and remounted by a different user without prompting for the password
Description: A logic issue was addressed with improved state management.
CVE-2019-8522: Colin Meginnis (@falc420)
FaceTime
Available for: macOS Mojave 10.14.3
Impact: A user’s video may not be paused in a FaceTime call if they exit the FaceTime app while the call is ringing
Description: An issue existed in the pausing of FaceTime video. The issue was resolved with improved logic.
CVE-2019-8550: Lauren Guzniczak of Keystone Academy
Feedback Assistant
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to gain root privileges
Description: A race condition was addressed with additional validation.
CVE-2019-8565: CodeColorist of Ant-Financial LightYear Labs
Feedback Assistant
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to overwrite arbitrary files
Description: This issue was addressed with improved checks.
CVE-2019-8521: CodeColorist of Ant-Financial LightYear Labs
file
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted file might disclose user information
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-6237: an anonymous researcher
Graphics Drivers
Available for: macOS Mojave 10.14.3
Impact: An application may be able to read restricted memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8519: Aleksandr Tarasikov (@astarasikov), Juwei Lin (@panicaII), and Junzhi Lu of Trend Micro Research working with Trend Micro’s Zero Day Initiative
iAP
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2019-8542: an anonymous researcher
IOGraphics
Available for: macOS Mojave 10.14.3
Impact: A Mac may not lock when disconnecting from an external monitor
Description: A lock handling issue was addressed with improved lock handling.
CVE-2019-8533: an anonymous researcher, James Eagan of Télécom ParisTech, R. Scott Kemp of MIT, and Romke van Dijk of Z-CERT
IOHIDFamily
Available for: macOS Mojave 10.14.3
Impact: A local user may be able to cause unexpected system termination or read kernel memory
Description: A memory corruption issue was addressed with improved state management.
CVE-2019-8545: Adam Donenfeld (@doadam) of the Zimperium zLabs Team
IOKit
Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A local user may be able to read kernel memory
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8504: an anonymous researcher
IOKit SCSI
Available for: macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: An application may be able to execute arbitrary code with kernel privileges
Description: A memory corruption issue was addressed with improved input validation.
CVE-2019-8529: Juwei Lin (@panicaII) of Trend Micro
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A remote attacker may be able to cause unexpected system termination or corrupt kernel memory
Description: A buffer overflow was addressed with improved size validation.
CVE-2019-8527: Ned Williamson of Google and derrek (@derrekr6)
Kernel
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
Impact: Mounting a maliciously crafted NFS network share may lead to arbitrary code execution with system privileges
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2019-8508: Dr. Silvio Cesare of InfoSect
Kernel
Available for: macOS Mojave 10.14.3
Impact: An application may be able to gain elevated privileges
Description: A logic issue was addressed with improved state management.
CVE-2019-8514: Samuel Groß of Google Project Zero
Kernel
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to determine kernel memory layout
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8540: Weibo Wang (@ma1fan) of Qihoo 360 Nirvan Team
Kernel
Available for: macOS Mojave 10.14.3
Impact: A local user may be able to read kernel memory
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-7293: Ned Williamson of Google
Kernel
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to determine kernel memory layout
Description: An out-of-bounds read issue existed that led to the disclosure of kernel memory. This was addressed with improved input validation.
CVE-2019-6207: Weibo Wang of Qihoo 360 Nirvan Team (@ma1fan)
CVE-2019-8510: Stefan Esser of Antid0te UG
Messages
Available for: macOS Mojave 10.14.3
Impact: A local user may be able to view sensitive user information
Description: An access issue was addressed with additional sandbox restrictions.
CVE-2019-8546: ChiYuan Chang
Notes
Available for: macOS Mojave 10.14.3
Impact: A local user may be able to view a user’s locked notes
Description: An access issue was addressed with improved memory management.
CVE-2019-8537: Greg Walker (gregwalker.us)
PackageKit
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to elevate privileges
Description: A logic issue was addressed with improved validation.
CVE-2019-8561: Jaron Bradley of Crowdstrike
Perl
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: Multiple issues in Perl
Description: Multiple issues in Perl were addressed in this update.
CVE-2018-12015: Jakub Wilk
CVE-2018-18311: Jayakrishna Menon
CVE-2018-18313: Eiichi Tsukata
Power Management
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: Multiple input validation issues existed in MIG generated code. These issues were addressed with improved validation.
CVE-2019-8549: Mohamed Ghannam (@_simo36) of SSD Secure Disclosure (ssd-disclosure.com)
QuartzCore
Available for: macOS Mojave 10.14.3
Impact: Processing malicious data may lead to unexpected application termination
Description: Multiple memory corruption issues were addressed with improved input validation.
CVE-2019-8507: Kai Lu of Fortinet’s FortiGuard Labs
Security
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: An application may be able to gain elevated privileges
Description: A use after free issue was addressed with improved memory management.
CVE-2019-8526: Linus Henze (pinauten.de)
Security
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to read restricted memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8520: Antonio Groza, The UK’s National Cyber Security Centre (NCSC)
Siri
Available for: macOS Mojave 10.14.3
Impact: A malicious application may be able to initiate a Dictation request without user authorization
Description: An API issue existed in the handling of dictation requests. This issue was addressed with improved validation.
CVE-2019-8502: Luke Deshotels of North Carolina State University, Jordan Beichler of North Carolina State University, William Enck of North Carolina State University, Costin Caraba? of University POLITEHNICA of Bucharest, and R?zvan Deaconescu of University POLITEHNICA of Bucharest
Time Machine
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.3
Impact: A local user may be able to execute arbitrary shell commands
Description: This issue was addressed with improved checks.
CVE-2019-8513: CodeColorist of Ant-Financial LightYear Labs
TrueTypeScaler
Available for: macOS Mojave 10.14.3
Impact: Processing a maliciously crafted font may result in the disclosure of process memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2019-8517: riusksk of VulWar Corp working with Trend Micro Zero Day Initiative
XPC
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.3
Impact: A malicious application may be able to overwrite arbitrary files
Description: This issue was addressed with improved checks.
CVE-2019-8530: CodeColorist of Ant-Financial LightYear Labs
Kennt jemand eigentlich einen „Geheimtipp“, wo man gut gebrauchte Mac Hardware kaufen kann?
Würde gerne einen Mac von 2012/2013 kaufen.
pssst: https://www.ebay-kleinanzeigen.de/
Hmnkay, ich würde ja „Danke“ sagen, fühle mich aber nicht danach….
Gibt es eine Möglichkeit nun noch an die Version 10.14.3 zu kommen? Ich benötige diese und finde momentan keinen Weg.